MetaServer > Help > How to run the MetaServer Service under a Non-Admin User
How to run the MetaServer Service under a Non-Admin User
IMPORTANT: Everytime you change the user rights of the account you use to run the MetaServer service, you need to restart the MetaServer Service to apply them.
For ultimate security and control, you may consider to run the MetaServer service under a specific non-admin account (= a standard Domain User account).
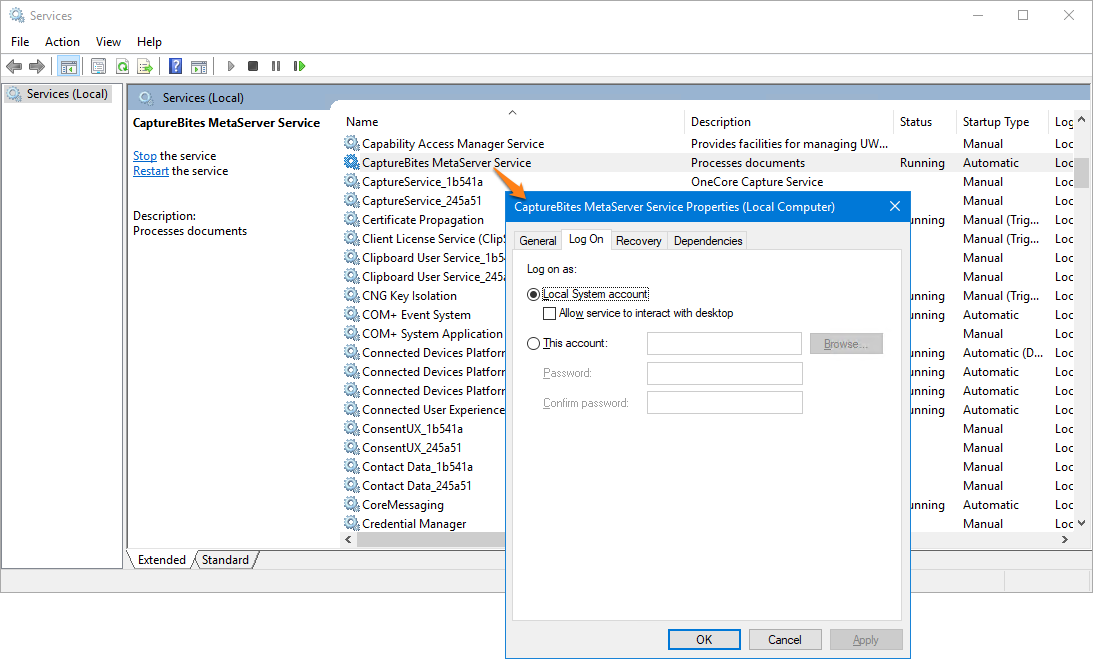
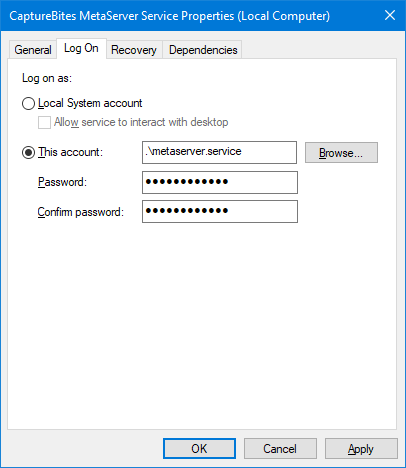
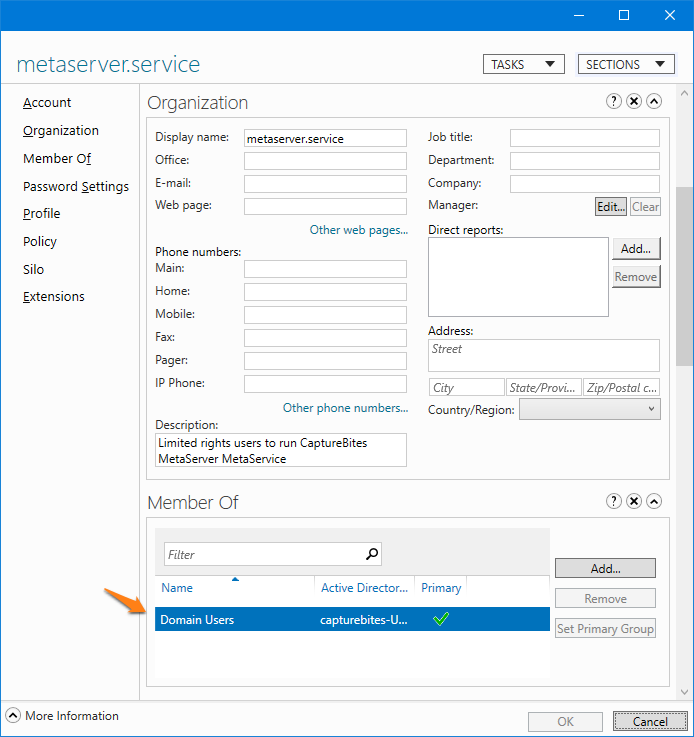
In our example, we have created a special user called “metaserver.service” and we want the MetaServer service to run under that account:
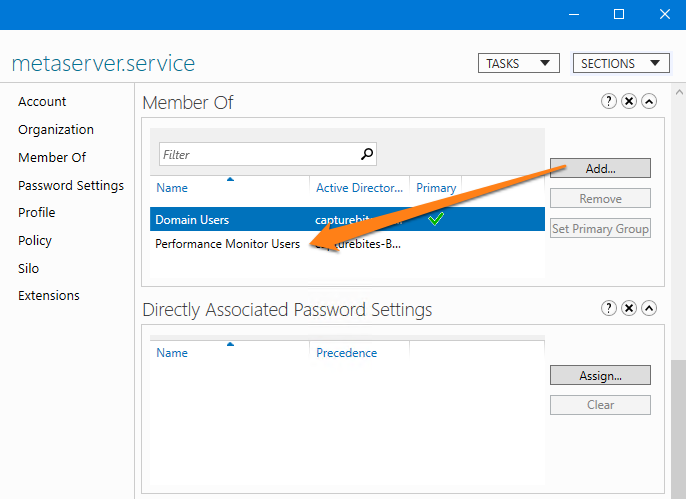
Step 1: as you can see below, the “metaserver.service” user we have created only has basic Domain User non-admin rights.
To make the service work, this user needs full access to the following folders and their subfolders:
C:\ProgramData\CaptureBites\Programs
C:\CaptureBites
Access to these two folders are critical to be able to start the service. Without access, the service won’t even start.
Step 2: provide full access to your import folders and output folders. Once you gave access to above folders, the service will start, but an error is generated in the following folder:
C:\ProgramData\CaptureBites\Programs\MetaServer\Data\Log\YYYY\MM
Example error:
“HTTP could not register URL http://+:8733/CaptureBites/MetaServer/Services/ServerInfoService/. Your process does not have access rights to this namespace (see https://go.microsoft.com/fwlink/?LinkId=70353 for details)”
Step 3: to avoid these errors, you need to give the user access rights to the namespaces:
http://+:8733/CaptureBites/MetaServer/Services/ServerInfoService/
http://+:8733/CaptureBites/MetaServer/Services/DatabaseService/
http://+:8733/CaptureBites/MetaServer/Services/LicenseService/
http://+:8733/CaptureBites/MetaServer/Services/WorkflowService/
http://+:8733/CaptureBites/MetaServer/Services/TransferService/
You do so by using the Microsoft “Netsh.exe” tool. You can find more info about “Netsh.exe” here:
https://docs.microsoft.com/en-us/dotnet/framework/wcf/feature-details/configuring-http-and-https?redirectedfrom=MSDN
IMPORTANT: in the commands below, make sure you use the correct domain and username in in the “user=” parameter.
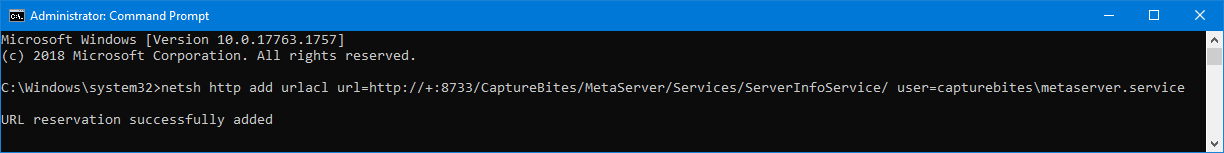
Run an elevated command prompt and run the following Netsh.exe commands to provide access to services required by MetaServer:
netsh http add urlacl url=http://+:8733/CaptureBites/MetaServer/Services/ServerInfoService/ user=capturebites\metaserver.service
netsh http add urlacl url=http://+:8733/CaptureBites/MetaServer/Services/DatabaseService/ user=capturebites\metaserver.service
netsh http add urlacl url=http://+:8733/CaptureBites/MetaServer/Services/LicenseService/ user=capturebites\metaserver.service
netsh http add urlacl url=http://+:8733/CaptureBites/MetaServer/Services/WorkflowService/ user=capturebites\metaserver.service
netsh http add urlacl url=http://+:8733/CaptureBites/MetaServer/Services/TransferService/ user=capturebites\metaserver.service
After you run these commands, you should get a confirmation message “URL reservation successfully added”:
These access rights are persistent and you do not have to run these commands again after rebooting the server.
NOTE: If you want to remove the user access rights, please follow the instructions below.
Step 5 (if applicable): if you come across the error “The format of the specified network name is not valid. Metaserver not found.”, you can run the following Netsh.exe command:
netsh http add iplisten +:8733
If, by accident, you gave access rights to the wrong user for a service and then try to run the command again with the correct user, you will get an error:
Url reservation add failed, Error: 183
Cannot create a file when that file already exists.
If you want to give access rights to another user to the service and the port, you need to delete the previous reservation first.
For example, to delete the reservation for the TransferService on port 8733, run the elevated command:
netsh http delete urlacl url= http://+:8733/CaptureBites/MetaServer/Services/TransferService/
After that you can run the “add access rights” command again to give access rights to the correct user for that service.
If you don’t know how to add access rights to your service, please refer to the above steps.
To list all access rights, run the elevated command:
netsh http show urlacl